Network access control
Prevent unauthorized access to your business network by enforcing access policies on devices that are connecting to the secure infrastructure. Implement secure cloud network access control with GoodAccess.
Create Free Account See DemoNo card needed. Full onboarding support.
BENEFITS
Full control over all inbound and outbound connections

Mitigate zero-day threats
Prevent unauthorized access to your infrastructure and monitor all ongoing inbound connections.
Main benefit

Manage access centrally
Control all user accounts, access permissions, and systems centrally. Bundle access permissions on virtual access cards.
Main benefit

Connect from anywhere
A 100% SaaS-delivered global infrastructure. Connect from anywhere to any company resource securely and with ease.
Main benefit
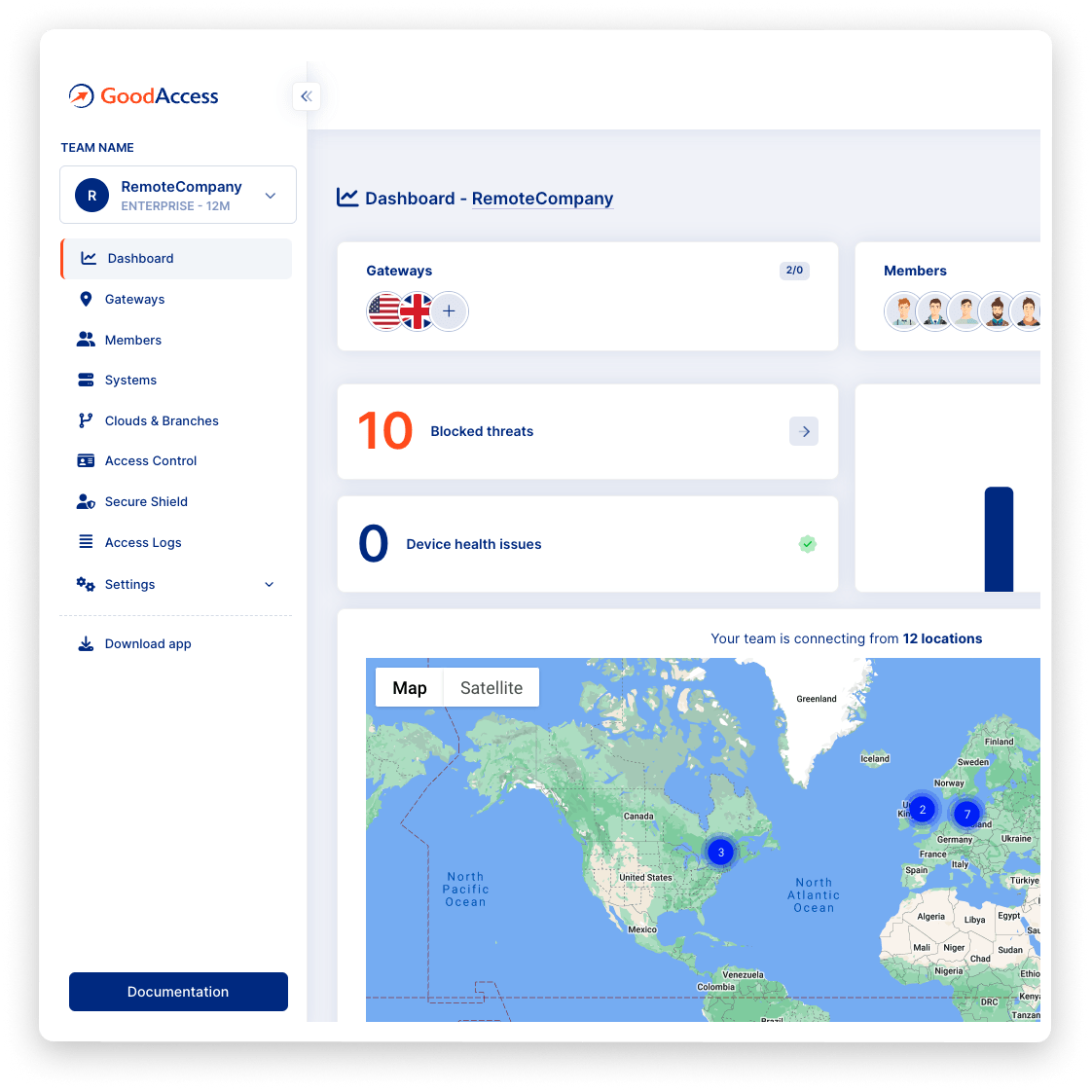
Try Interactive Demo
Experience GoodAccess via an interactive demo. Get a feel for all its features and find out why GoodAccess is the right choice for your business.
Network access control demo
How to use network access control
FEATURES
GoodAccess NAC is access control for the networkless company
MFA
Identity-based authentication
Prevent threat intrusion by pre-authenticating users on the application and network level before they interact with business systems. Reinforce the login with multi-factor authentication (MFA) and biometrics.
Access cards
Web-based central management
Manage all users, access privileges, and connections to company systems from a user-friendly web-based interface. Virtual access cards can be used to assign access rights per role, allowing for quick and easy access management.
goodaccess apps
Mobile and desktop client apps
Client apps are available for MacOS, iOS, Windows, and Android to simplify the authentication of user devices and connect them to the secure global infrastructure.
dedicated gateway
Dedicated gateway with a static IP
Connect to a gateway nearest to your location via a secure encrypted tunnel to shield your data from eavesdropping and other online threats. Use the gateway's static IP to restrict network access, speed up cloud access by IP whitelisting, or publish your customer-facing services online.
private network
Worldwide private network
Connect to your nearest gateway from any network, whether home, office, or café, via a private encrypted tunnel, and shield your connection from online threats. Choose from 35+ gateways distributed globally.
threat detection
Web-based threat detection
Enjoy automated protection from phishing attempts, malware-hosting sites, or productivity sinks. Your secure gateway contains a built-in DNS filter with multiple threat intelligence feeds.
no hardware needed
Zero hardware
GoodAccess is 100% SaaS-delivered, which means zero hardware. Set up network access control even if you don't have an IT person.
Case study
Hear it from your peers


Case study
Zero Trust Architecture in Creative Dock
Creative Dock needed to ensure ISO 27001 compliance, but they
struggled to achieve the required level of security and control over their network and
user devices (BYOD) with their prior remote-access solution.
Without any additional hardware, GoodAccess provided Creative Dock with full,
centralized control over their infrastructure and
covered up to 70% of technical security requirements of ISO 27001.

Trusted leader in Zero Trust Security
Discover why leading companies rely on GoodAccess for building their Zero Trust Architecture solutions.

"Incredibly user frienly, fast and very helpful."
Overall, the GoodAccess platform is amazing. From the administration side, the platform is incredibly user friendly and you can be up and running in a few minutes, managing users takes no time at all and the customer service is fast and very helpful. We have been with GoodAccess for a number of years with no complaints. The product is very competitive in price with its competitors.

"Find the connectivity and stability of connections stable."
We have been very happy with the reliability of GoodAccess. We find the connectivity and stability of connections stable, we have users across multiple countries and the experience has been very good.

"Simplifies access management and reduces network administration complexity."
GoodAccess's Zero Trust Architecture effectively secures our access to critical network infrastructure and web applications. By enabling a unified IP address for all clients, it simplifies access management and reduces network administration complexity.


"Secure, scalable access to critical systems across a global IP reach."
GoodAccess provides fast onboarding, excellent reporting, and helpful support. It offers secure, scalable access to critical systems across a global IP reach, making it vital for managing multiple users effortlessly. The platform's user-friendly management enhances our operational efficiency and security.

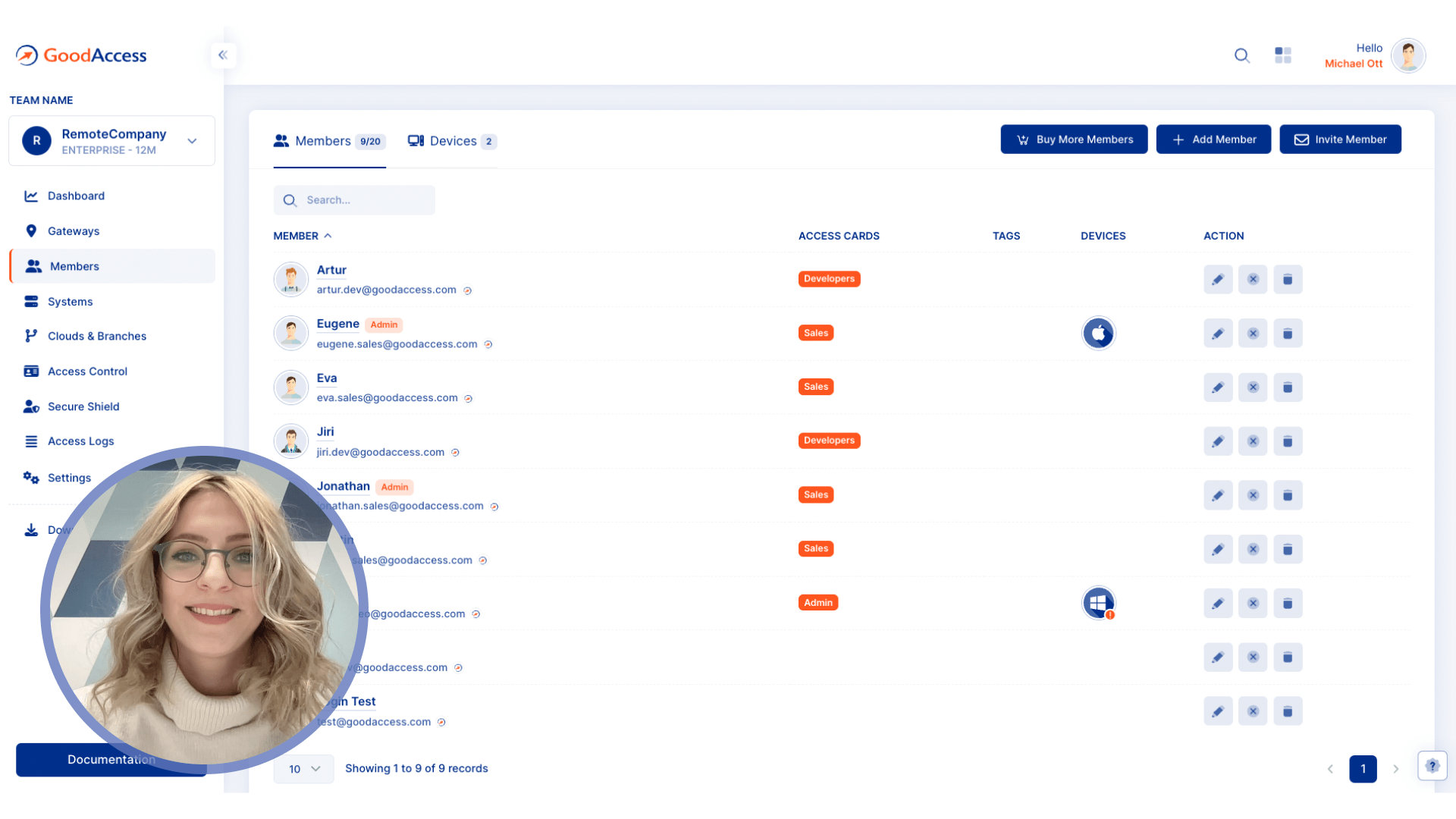
How to enable NAC in GoodAccess

Test all premium features for 14 days without limitation. No credit card required.

Connect to a gateway near your location, decide what systems to include in your secure environment

Invite team members and set up 2FA. Assign access cards with privileges to each user role.
No card needed. Full onboarding support.
Get your personalized product demo
Take a product tour with Eva, GoodAccess product expert, to discover how GoodAccess meets your needs firsthand.

Other features
Explore other features

Zero-trust access control
Minimize the attack surface by robust user authentication, granular privilege assignment, and strong encryption.


Dedicated VPN gateway
Connect from anywhere in the world via a secure and private tunnel.


Access Logs
Ensure compliance and create a detailed record of access history for post-compromise analysis.

Network access control guide
A complete guide to network access control
Network access control consists of several components:
-
Identity-based authentication and authorization
-
Traffic encryption on all networks
-
Policy definition and enforcement
Identity-based authentication and authorization
Unlike conventional networks, where endpoints and network devices are identified by an
IP address, NAC is identity-based. GoodAccess NAC pre-authenticates users by requiring
login credentials and, as a best practice, additional authentication factors, before
allowing them inside the secured infrastructure.
NAC often uses multi-factor authentication (MFA) to harden the authentication process
with more identity factors and further minimize the risk of unauthorized access.
Authentication extends to user devices as well. Each device has to prove the legitimacy
of its access. GoodAccess NAC uses client apps for desktop and mobile devices that users
install on their devices and log into the company infrastructure through them.
Traffic encryption on all networks
GoodAccess NAC enforces an equal level of security on all networks – whether
company-owned, employee-owned, or completely public. Users connect from any location to
an access gateway through a secure encrypted tunnel (via the OpenVPN or IKEv2 protocol),
which conceals their identity and the data they send.
This significantly reduces the risk of malware intrusion or man-in-the-middle attacks
when connecting from unsecured networks.
Policy definition and enforcement
Security policy definition and enforcement in NAC deals with the assignment of access
privileges. GoodAccess uses virtual access cards that allow you to manage access rights
easily and centrally.
An access card represents the privileges that employees of a given role need to do their
work. You can define access cards for developers, sales people, marketing team,
administrators, etc., and assign those to real employee accounts to allow access to
those systems.
This is an elegant way to define and manage your access policy, which can be changed in
the GoodAccess web interface by just one click of the mouse.
For more information on network access control check this article or visit our support portal for a hands-on guide.

