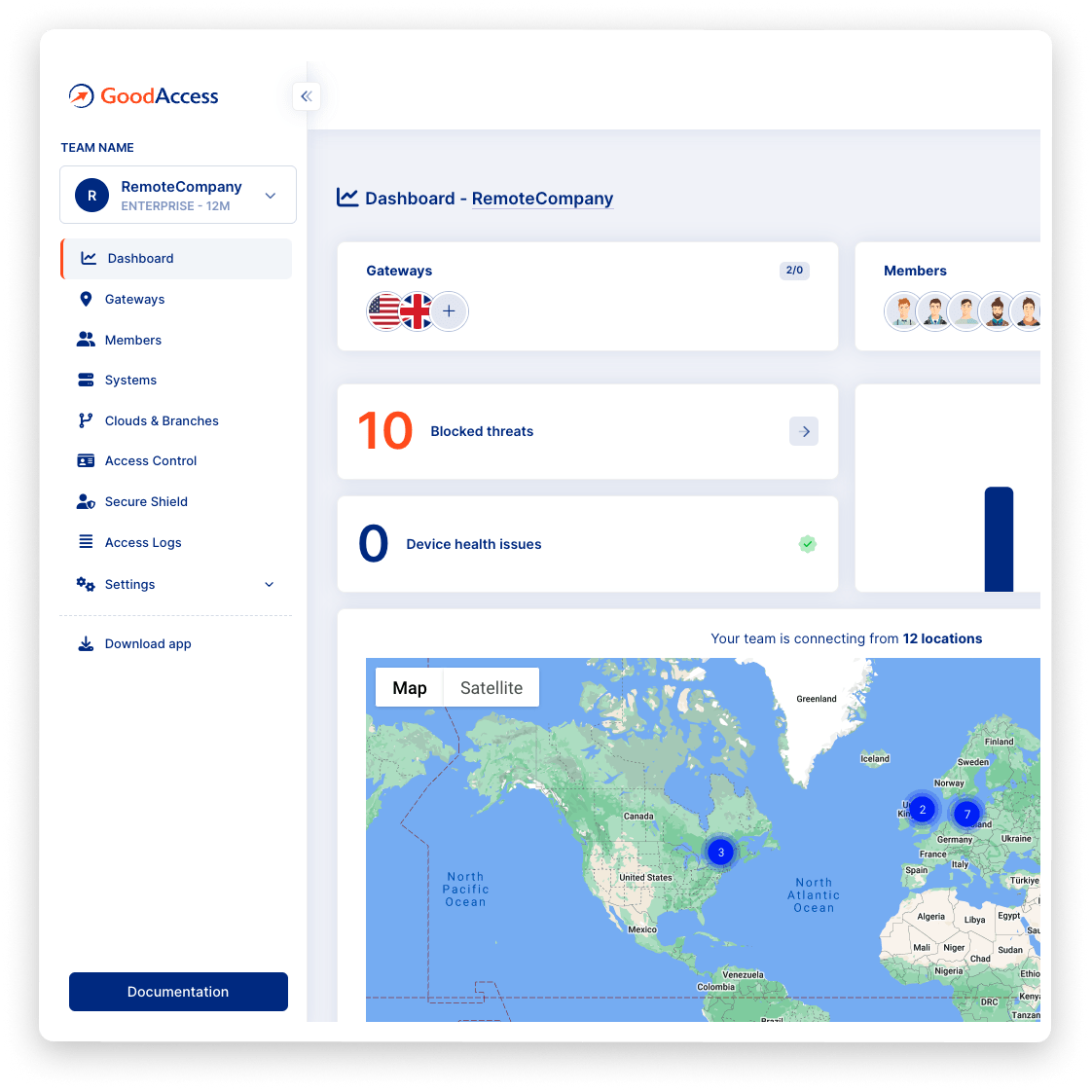
Zero Trust Network Access Made Simple
Create a secure virtual network between all users, networks, clouds, and on-prem resources. Get started in 10 minutes. Scale easily. 100% cloud zero-trust network access solution designed for small and medium businesses.
Create Free Account See DemoNo card required. Full onboarding support.




BENEFITS
Provision secure cloud access to business resources. Anytime, anywhere.

Secure
Create a bulletproof defense against breaches with identity based access rules, traffic encryption, MFA, SSO, network segmentation, and other features.

User-friendly
Tap into the resilient network as a service. Operate your own virtual infrastructure with a few clicks through a web interface. High-speed connectivity, anywhere, anytime.

Designed for SMBs
Cut the costs of network security and operations. Get started in 10 minutes with no expert skills needed. 100% cloud solution that scales as your business grows.

Loved by users
Walkthroughs, user guides, top-rated support, and user experience result in an average 4.8/5 user satisfaction rating and 92% likelihood to recommend GoodAccess.
Try Interactive Demo
Experience GoodAccess via an interactive demo. Get a feel for all its features and find out why GoodAccess is the right choice for your business.
FEATURES
Multi-layered security for the network-less organizations
With access rules, strong authentication, segmentation, and more you can level up your security across on-site and remote locations.
branch connectors
Cloud & branch connectors
The built-in cloud and branch connector enables you to connect your clouds, data centers, and private LANs into your GoodAccess virtual infrastructure easily and securely. You can choose what protocols to use (IPsec, IKEv2, or OpenVPN) depending on your preference or the environment. If you need highly available remote access to your on-prem or cloud systems, you can set up a redundant IPsec or IKEv2 tunnel as a failsafe.
Single sign-on
SSO & Identity management
Simplify identity management and access control with single sign-on (SSO). GoodAccess supports SSO with access credentials from Microsoft Entra ID, Google Workspace, Okta, and other SAML compatible services. SCIM for automated access provisioning is also supported.
threat blocker
Breach prevention
Threat Blocker is a native, always-on feature of GoodAccess that prevents users from accessing dangerous or compromised malicious websites and falling prey to malware, phishing, command and control (C&C) botnets and other ploys. Protection is constantly updated using threat intelligence feeds and DNS blacklists (see DNS filtering).
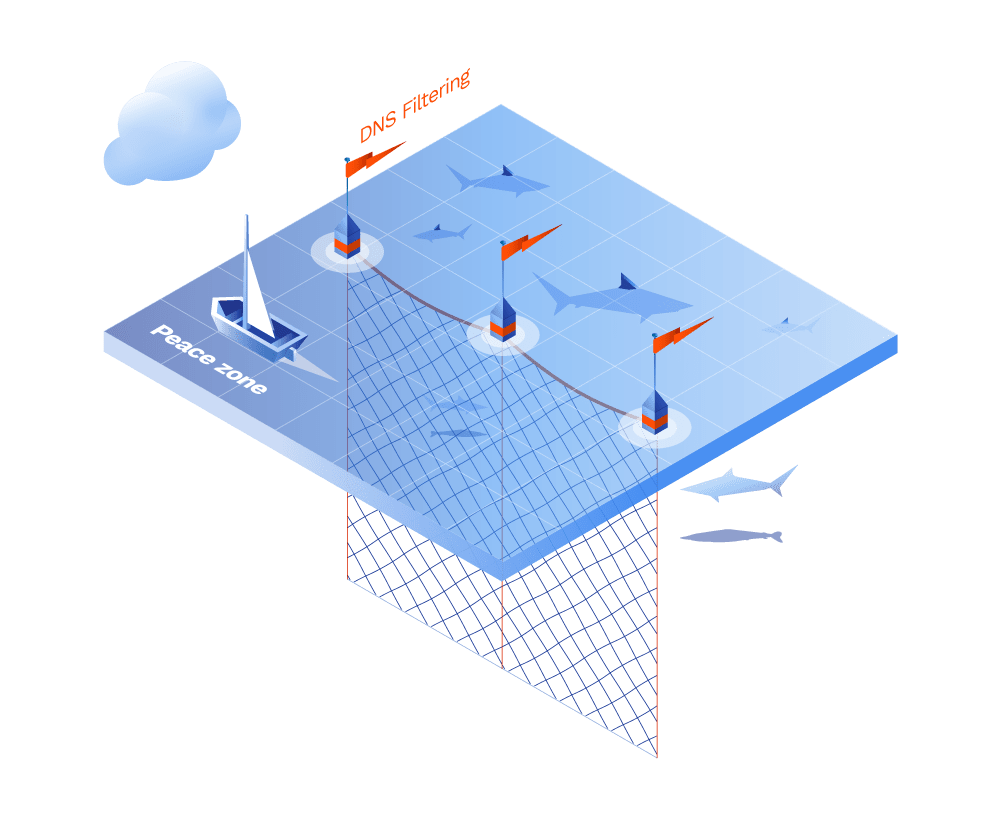
DNS FILTERING
Network Control & Visibility
GoodAccess DNS filtering gives you control over access to all sites and applications so that you can automatically restrict unwanted user behavior and block phishing and other malicious domains.
Access logs
User activity logging
Have full control over gateway access points to monitor who and when connects to your network. This will help you to reduce risk and comply with GDPR, SOC2, or HIPAA regulations.
two/Multi factor authentication
2FA/MFA on the network layer
GoodAccess allows enforcing 2FA/MFA for admin login as well as for users' login to GoodAccess app. Instead of labor-intensive configuration of MFA for each application, you can unify authentication on the network level with GoodAccess. This works even if your systems don't support 2FA/MFA on the application level.
virtual access cards
Centralized access control
Segment your network and assign permissions on the least-privilege principle to prevent unauthorized access. With virtual access cards you can determine which user may access which system. As a result, every user has a private account and network identity so they are allowed to access only specified applications. You can also use external providers' single-sign-on authentication (GSuite, Okta, Active Directory/LDAP).
The best priced offering on the market
100% cloud ZTNA solution that scales as your business grows.
Dedicated Cloud VPN with Static IP whitelisting
Dedicated ZTNA Architect.
Networking
Clouds & Branch connectors
Access systems in your office LAN or private/public cloud from anywhere. One connector is included and more can be purchased as an add-on.
Custom domain names
Set up custom private DNS records for your systems.
Site-to-site connectivity
Interconnect multiple clouds or local networks through a secure tunnel.
Forced Always-on
Ensure your users are protected at all times and prevent them from disconnecting from the GoodAccess network.
Premium SECURE SHIELD
Device posture check
Enforce device compliance with your organization's security policies by automatically checking them before allowing access to your network perimeter and protected resources.
Zero Trust Access Control
Reduce your attack surface and provide secure access for your employees regardless of their location.
Single sign-on (SSO)
Use or combine various identity providers such as Google, MS Entra ID, Okta, and other SAML-compatible services for SSO.
SCIM
Avoid human error and streamline your user onboarding and offboarding via SCIM provisioning.
Custom domain blocking
Block custom domains that you don't want your employees to visit, e.g. social networks or adult content.
System-level access logs
Monitor user-application interactions and meet compliance requirements (GDPR, HIPAA, SOC2, NIS2).
Support
Priority chat and email support
Priority problem resolution service from our experts.
Enterprise features and Premium 24/7 support for large organizations
SOC2 and ISO 27001 certified. GDPR, HIPAA compliant.
GoodAccess adheres to the most demanding standards of software security compliance so you can have a peace of mind that your organization's data is safeguarded properly.
Let's get started

Create your free account and get all premium features for 14 days for free.

Choose from 35+ locations for your dedicated gateway. Connect your systems, apps, clouds and devices.

Invite users via email to create their account and get the GoodAccess app. Use Access Cards to assign permissions only to particular SaaS applications, services, servers, internal systems and such.

securely
Click to connect from any device anywhere and work securely. Oversee who and when connects to your applications, control activity and data transfers.
Get your personalized product demo
Take a product tour with Eva, GoodAccess product expert, to discover how GoodAccess meets your needs firsthand.

FAQs
Zero trust network is a network that by design minimizes insider threats and prevents risks associated with unauthorized access/credential misuse. This is achieved by very strict access verification and damage containment via restriction of unnecessary access privileges - so-called the least privilege principle.
The main difference is in the scope of access rights provided to the user. A VPN allows user access to the entire network once they are authorized. Zero trust network access is a security concept utilizing the least privilege principle, so that access is granted only to selected systems for satisfactorily authorized users.
Any company, no matter the size can today implement zero-trust network access security thanks to the democratization of ZTNA tools. Basically, there are three forms that a ZTNA deployment can take and they vary depending on the systems included and the overall goals they aim to achieve: identity-based model, microsegmentation model, and software-defined perimeter (SDP). Learn more about the ZTNA implementation in our blog.

