Software-defined perimeter
Make your infrastructure invisible to the prying eyes of attackers and other non-authorized personnel, whether it resides in your LAN, datacenter, or cloud. With GoodAccess software-defined perimeter you can define your network with identity-based network access and face modern online threats with confidence.
Create Free Account See DemoNo card required. Full onboarding support.




BENEFITS
Cloak your IT assets

Secure
Cover every device as a potential entry point to your network and protect it by zero-trust access control, MFA, SSO, traffic encryption, segmentation, and other features.

Easy to manage
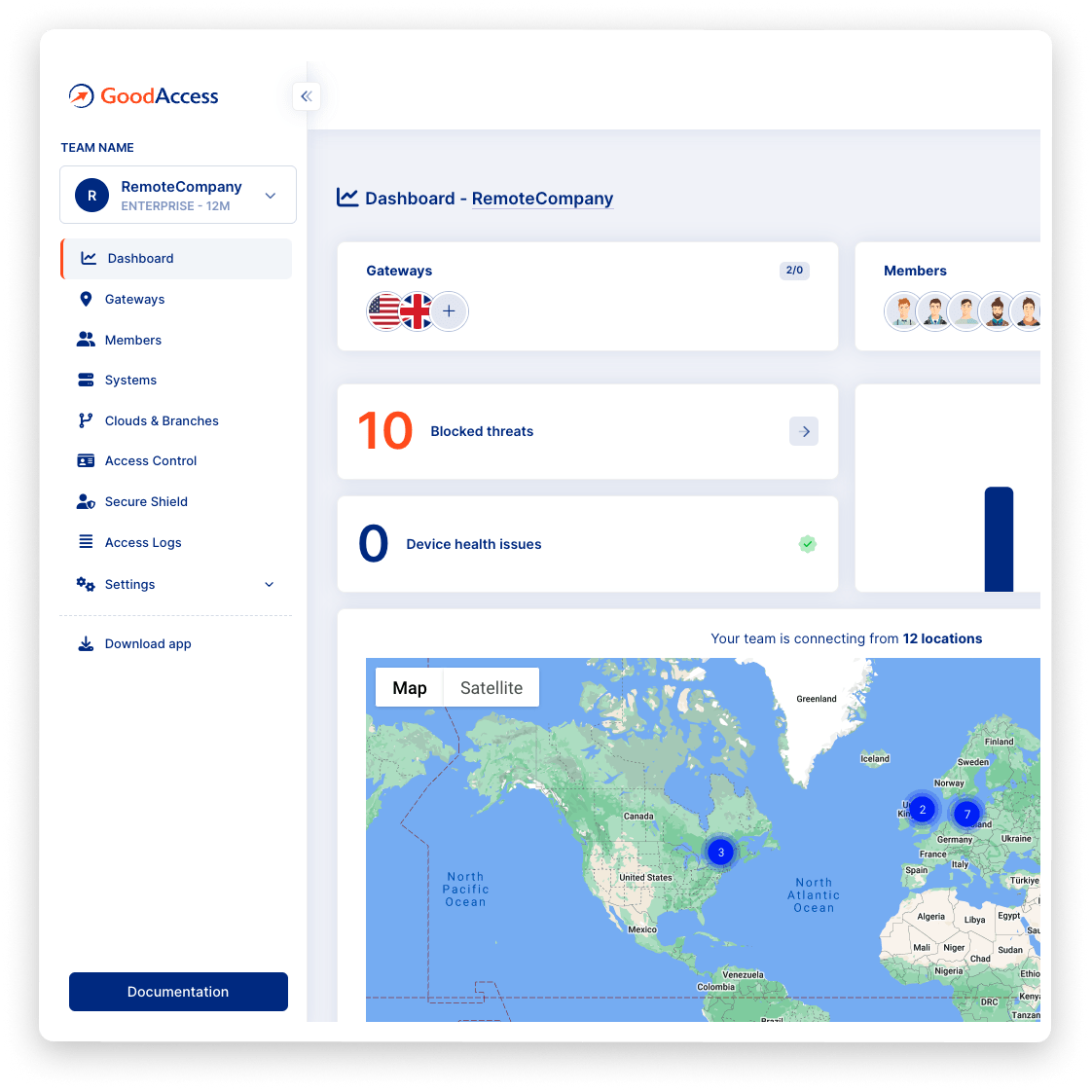
Manage on-premise and cloud assets, users and devices, assign access rights, and set up granular access policies via a web GUI.

Cloud delivered
Deploy GoodAccess in 10 minutes even if you are not a networking expert. Benefit from a 100% software solution that scales as you grow.

Loved by users
Walkthroughs, user guides, top-rated support, and user experience result in an average 4.8/5 user satisfaction rating and 92% likelihood to recommend GoodAccess.
Try Interactive Demo
Experience GoodAccess via an interactive demo. Get a feel for all its features and find out why GoodAccess is the right choice for your business.
FEATURES
All you need to build a bulletproof software-defined perimeter
secure gateway
Secure web gateway
Prevent users from accessing dangerous or compromised malicious websites and falling prey to malware, phishing, command and control (C&C) botnets and other ploys. Once a user connects through a GoodAccess cloud gateway with your dedicated DNS server, all of their web activity is protected in real time by blocking unwanted content and malicious domains. Protection is constantly updated using threat intelligence feeds and DNS blacklists (see DNS filtering).

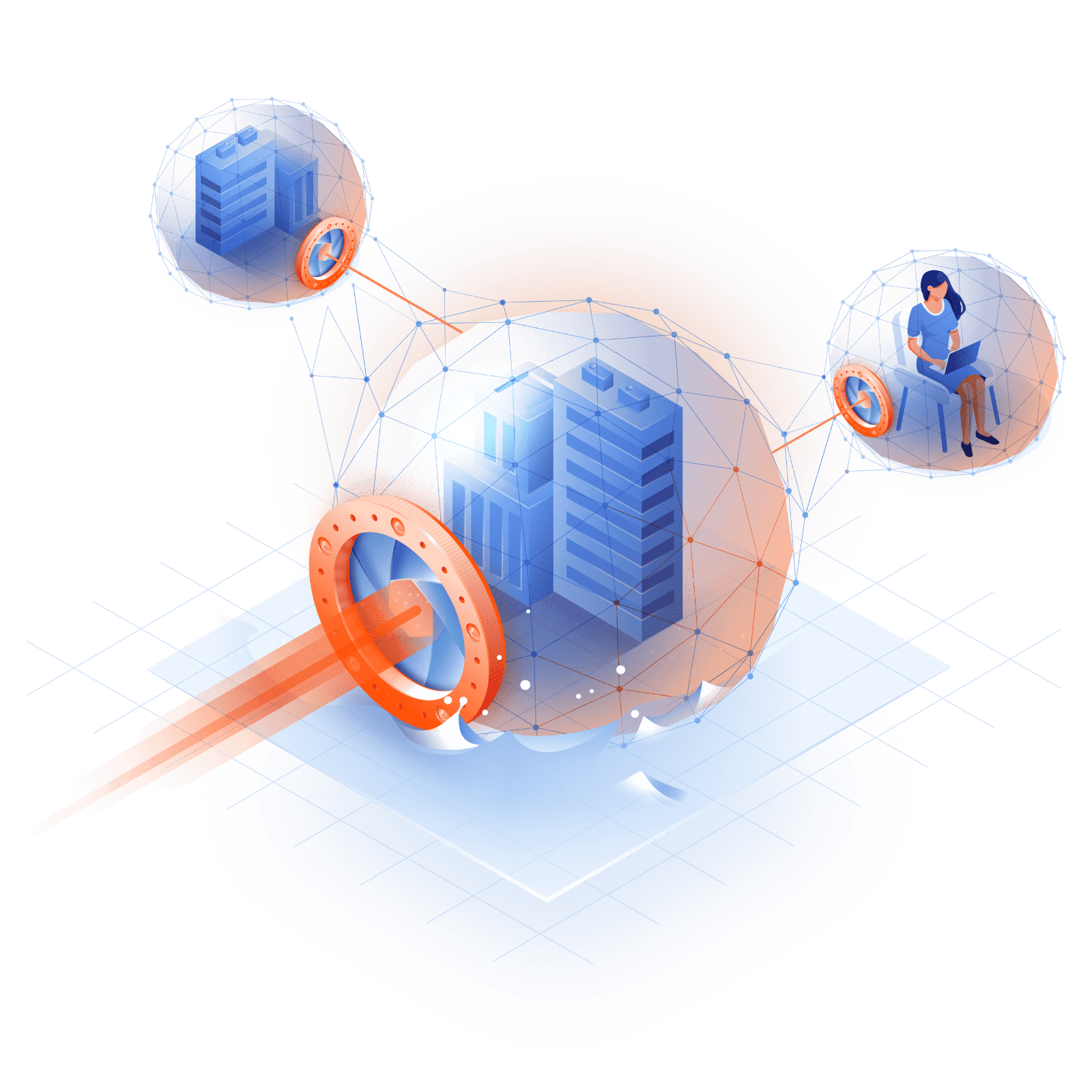
branch connector
Cloud & branch connector
Incorporate your network resources in a few minutes with no reconfiguration of your current infrastructure. Include any on-premise infrastructure (LANs, data centers) or clouds into a software defined perimeter with GoodAccess connectors to hide them on the public internet. Choose what protocols to use (IPsec, IKEv2, or OpenVPN) to establish an encrypted connection and set up a redundant IPsec or IKEv2 tunnel as a failsafe.
threat blocker
Zero-trust access control
Assign access rights based on the least-privilege principle to prevent unauthorized access and lateral movement. With virtual access cards, every user receives a private network identity, which, after authentication, allows them to access only specified applications that they are authorized to use. You can also use external providers' single sign-on authentication (GSuite, Okta, Active Directory/LDAP).
user-to-application
Segmentation on an application level
With GoodAccess' software defined perimeter you can control access on a user-to-application basis. Define your SaaS based application such as CRM and marketing tools as part of your secured network and apply the same level of protection as in your LAN in a few clicks. By segmenting access rights in the GoodAccess management dashboard, you achieve a higher granularity than network segmentation at a fraction of network operation costs and deployment time.
device access
Access from any device
GoodAccess comes with always-on client apps for iOS, macOS, Android, Windows and ChromeOS. No configuration is needed. Once authenticated through the GA app, any device turns into a secure end-point. Just invite your colleagues via email to create their account and get the GoodAccess app.
MFA/SSO
Robust User Authentication (MFA/SSO)
Base access to your network resources on user identity and device posture check. GoodAccess pre-authenticates users and their devices when they log into the secure GoodAccess infrastructure. The login supports multi-factor authentication (MFA), biometrics and tokens on the top of single sign-on (SSO) using Google, Okta, MS Entra ID credentials, or universal (SAML). Automate your access provisioning via SCIM.
access monitoring
Compliance and policy enforcement
Have full control over gateway access points to monitor who connects to your network and when. See which users log into your systems, when, and how much data they transfer. Observe user access behavior to reduce risk and comply with GDPR, SOC2, or HIPAA regulations.
Case study
Hear it from your peers


Case study
Zero Trust Architecture in Creative Dock
Creative Dock needed to ensure ISO 27001 compliance, but they
struggled to achieve the required level of security and control over their network and
user devices (BYOD) with their prior remote-access solution.
Without any additional hardware, GoodAccess provided Creative Dock with full,
centralized control over their infrastructure and
covered up to 70% of technical security requirements of ISO 27001.

Trusted leader in Zero Trust Security
Discover why leading companies rely on GoodAccess for building their Zero Trust Architecture solutions.

"Incredibly user frienly, fast and very helpful."
Overall, the GoodAccess platform is amazing. From the administration side, the platform is incredibly user friendly and you can be up and running in a few minutes, managing users takes no time at all and the customer service is fast and very helpful. We have been with GoodAccess for a number of years with no complaints. The product is very competitive in price with its competitors.

"Find the connectivity and stability of connections stable."
We have been very happy with the reliability of GoodAccess. We find the connectivity and stability of connections stable, we have users across multiple countries and the experience has been very good.

"Simplifies access management and reduces network administration complexity."
GoodAccess's Zero Trust Architecture effectively secures our access to critical network infrastructure and web applications. By enabling a unified IP address for all clients, it simplifies access management and reduces network administration complexity.


"Secure, scalable access to critical systems across a global IP reach."
GoodAccess provides fast onboarding, excellent reporting, and helpful support. It offers secure, scalable access to critical systems across a global IP reach, making it vital for managing multiple users effortlessly. The platform's user-friendly management enhances our operational efficiency and security.

The best priced offering on the market
100% cloud SDP solution that scales as your business grows.
Dedicated Cloud VPN with Static IP whitelisting
Full onboarding support.
Networking
Clouds & Branch connectors
Access systems in your office LAN or private/public cloud from anywhere. One connector is included and more can be purchased as an add-on.
Custom domain names
Set up custom private DNS records for your systems.
Site-to-site connectivity
Interconnect multiple clouds or local networks through a secure tunnel.
Forced Always-on
Ensure your users are protected at all times and prevent them from disconnecting from the GoodAccess network.
Premium SECURE SHIELD
Device posture check
Enforce device compliance with your organization's security policies by automatically checking them before allowing access to your network perimeter and protected resources.
Zero Trust Access Control
Reduce your attack surface and provide secure access for your employees regardless of their location.
Single sign-on (SSO)
Use or combine various identity providers such as Google, MS Entra ID, Okta, and other SAML-compatible services for SSO.
SCIM
Avoid human error and streamline your user onboarding and offboarding via SCIM provisioning.
Custom domain blocking
Block custom domains that you don't want your employees to visit, e.g. social networks or adult content.
System-level access logs
Monitor user-application interactions and meet compliance requirements (GDPR, HIPAA, SOC2, NIS2).
Support
Priority chat and email support
Priority problem resolution service from our experts.
Zero-trust access for multi-site & cloud businesses
Enterprise features and Premium 24/7 support for large organizations
SOC2 and ISO 27001 certified. GDPR, HIPAA compliant.
GoodAccess adheres to the most demanding standards of software security compliance so you can have a peace of mind that your organization's data is safeguarded properly.
Let's get started

Create your free account and get all premium features for 14 days for free.

Choose from 35+ locations for your dedicated gateway. Define which assets should be part of your network, such as systems, apps, clouds, and devices.

Invite users via email to create their account and get the GoodAccess app. Use access cards to assign permissions only to selected SaaS applications, services, servers, internal systems, and such.

securely
Click to connect from any device anywhere and work securely. Oversee who and when connects to your applications, control activity, and data transfers.
Get your personalized product demo
Take a product tour with Eva, GoodAccess product expert, to discover how GoodAccess meets your needs firsthand.

FAQs
Software defined perimeter (SDP) is a security framework that allows hiding both traffic and the IT infrastructure connected to the public internet from interception. SDP interconnects all users (employees, third party) and company assets in a shielded environment on the network layer. This means it only establishes a connection once it has verified the identity of the user and determined if the user device meets the conditions for connecting. An authenticated user does not gain access to the entire network but only to systems they are authorized to work with.
The main difference is in the scope of access rights provided to the user. A VPN allows user access to the entire network once they are authorized. Zero trust network access is a security concept utilizing the least privilege principle, so that access is granted only to selected systems for satisfactorily authorized users.
Any company, no matter the size can today implement zero-trust network access security thanks to the democratization of ZTNA tools. Basically, there are three forms that a ZTNA deployment can take and they vary depending on the systems included and the overall goals they aim to achieve: identity-based model, microsegmentation model, and software-defined perimeter (SDP). Learn more about the ZTNA implementation in our blog.

