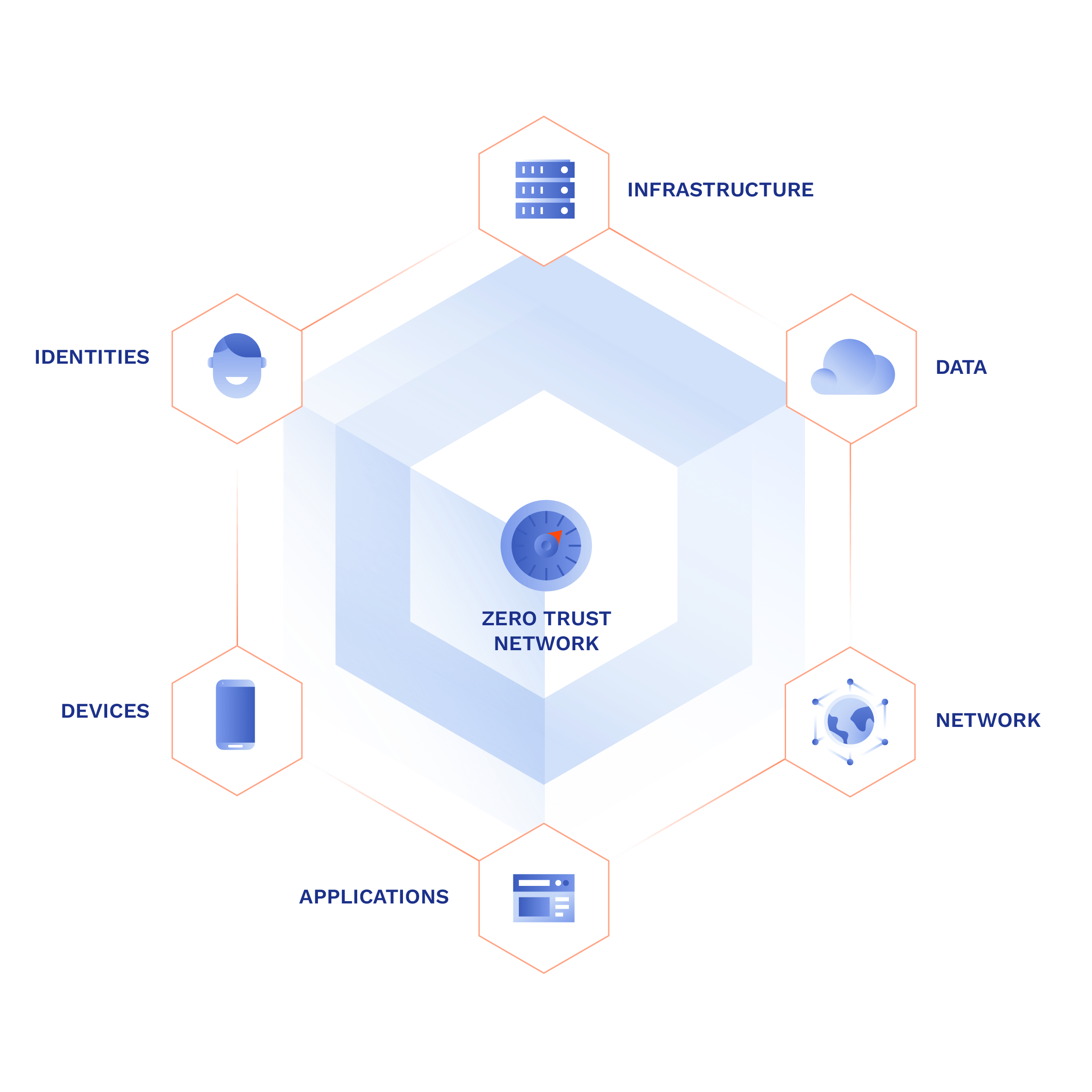
Zero-trust access control
Reduce the risk of unauthorized access to company systems by enforcing strong authentication, network and application-layer segmentation, and access logging. Enforce a uniform level of security across all your resources: on-premise, cloud, or hybrid. Zero-trust access control with no hardware required.
Create Free Account See Demo
Try zero-trust access control for free.
No card needed. Full onboarding support.
BENEFITS
Multi-layered security for the networkless organization

Reduce attack surface
Conceal end-users and resources from threat actors by establishing private user-to-system connections via a secure encrypted tunnel from any location.
Main benefit

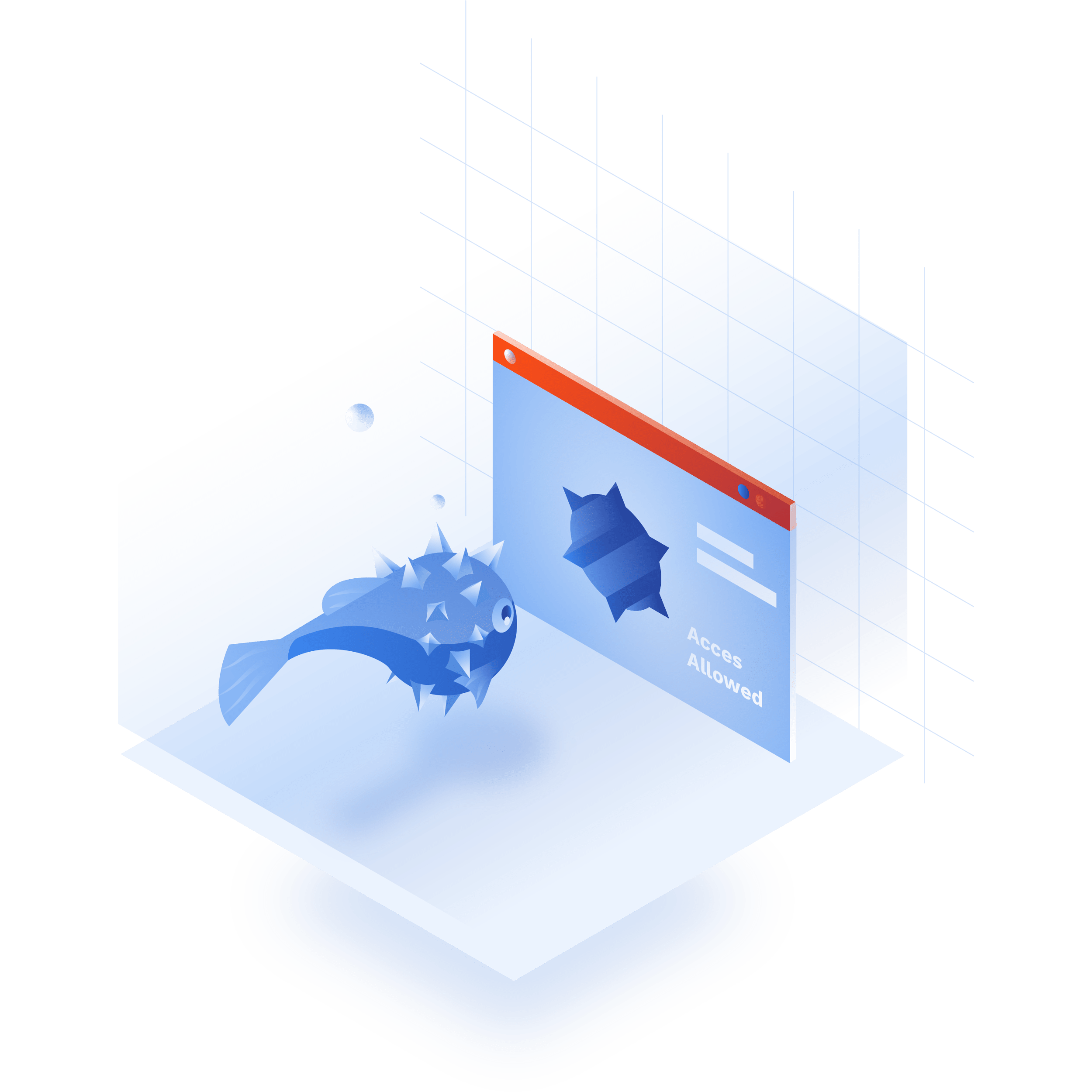
Prevent unauthorized access
Enforce strong authentication of both users and their devices on the network and application layer, and terminate them after each session.
Main benefit

Contain
threats
Least-privilege assignment of access rights ensures attackers cannot access all systems even if they succeed in penetrating one of them.
Main benefit
Try Interactive Demo
Experience GoodAccess via an interactive demo. Get a feel for all its features and find out why GoodAccess is the right choice for your business.
Zero-trust access control demo
How to use zero-trust access control?
FEATURES
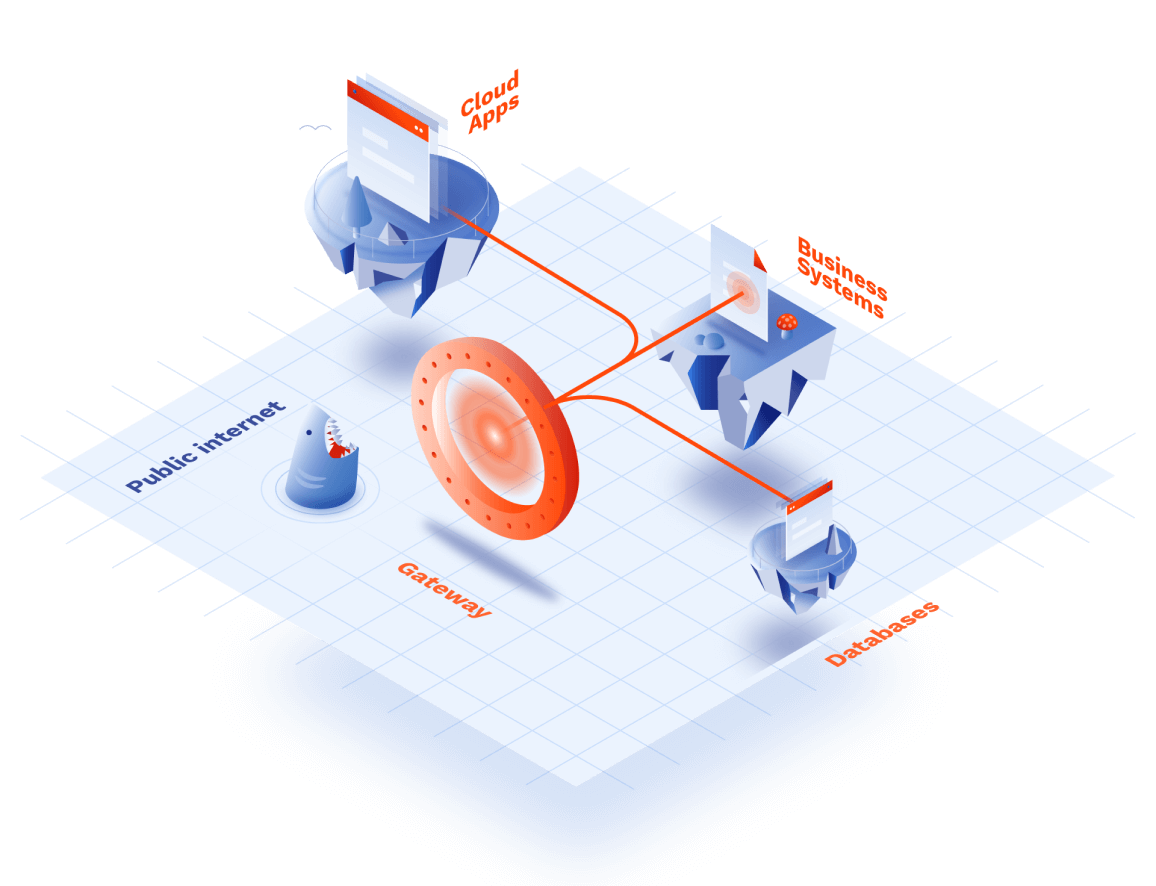
Provision secure cloud access to business resources
multi factor authentication
Identity-based authentication
Prevent threat intrusion by pre-authenticating users on the application and network level before they interact with business systems. Simplify access provisioning via SCIM integration and reinforce login with multi-factor authentication (MFA) and biometrics.
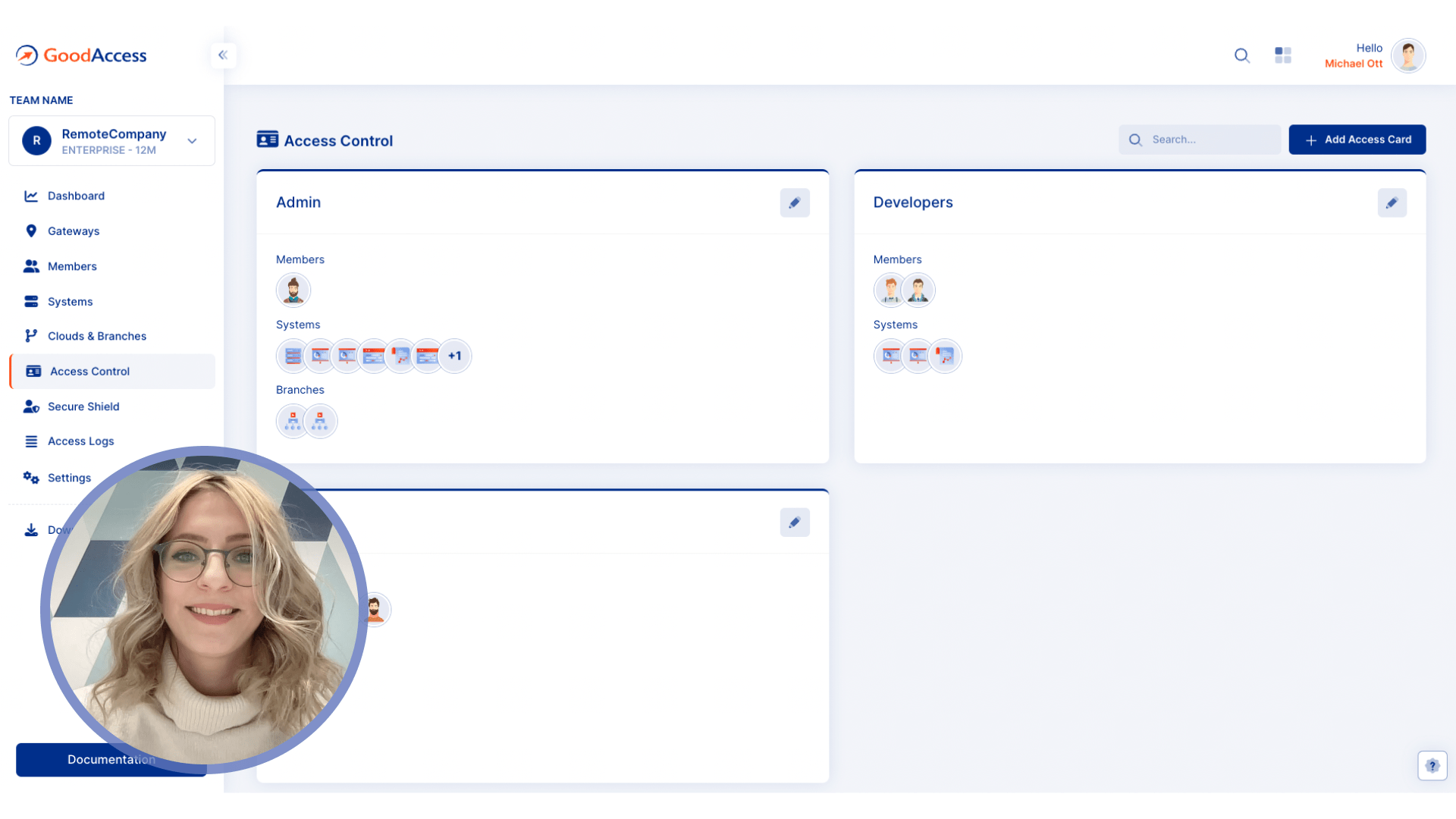
virtual access
Least-privilege access
Use virtual access cards to bundle access rights to allowed systems for each company role. Manage access cards centrally, assign or remove privileges for entire groups with just one click.
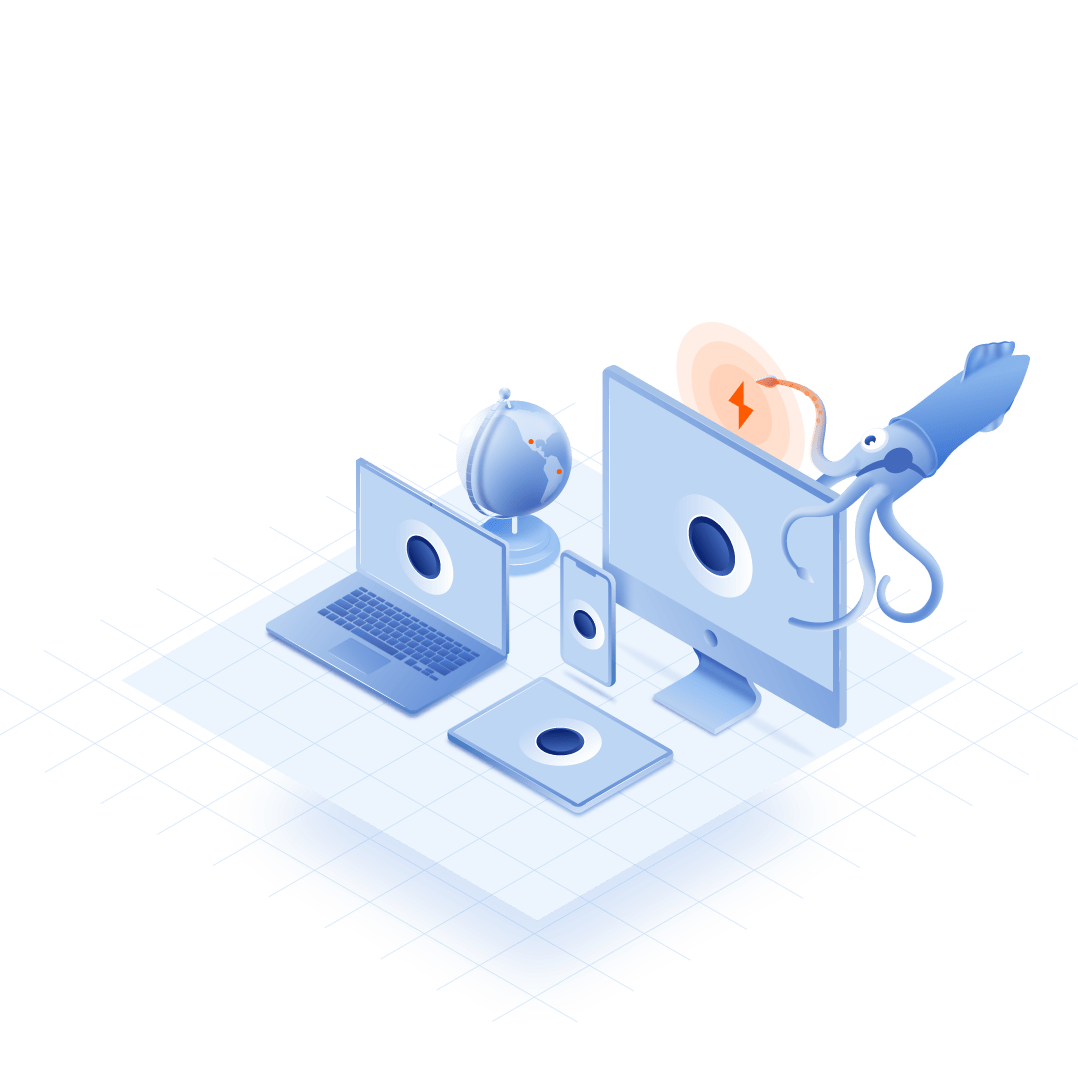
strong encryption
Identity obfuscation
Shield your systems and end-users by using strong encryption on the level of HTTPS and TCP headers and protect both your online identity and data. Establish connections on a per-session basis to further reduce your silhouette on the public internet.
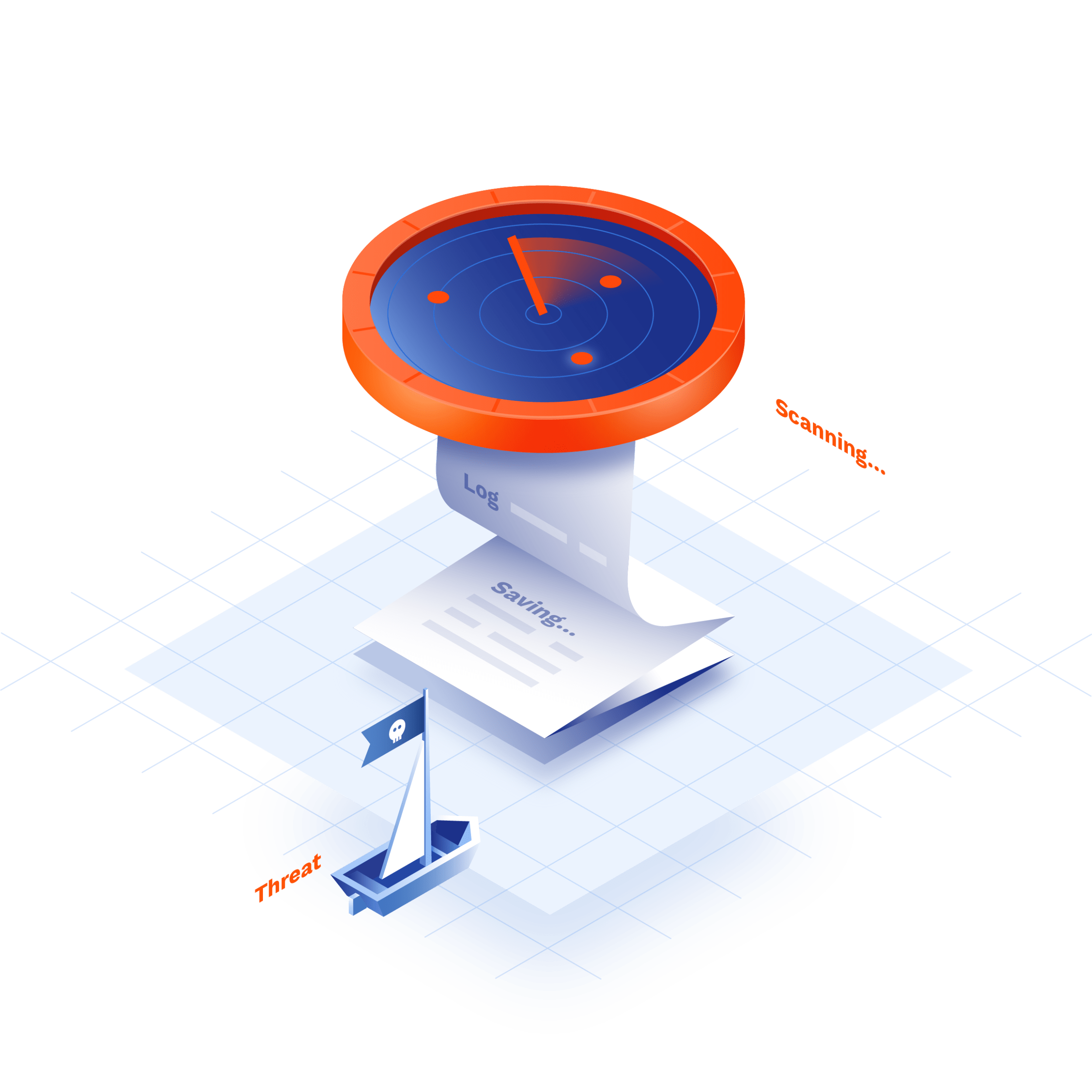
access logs
Access logging
Gather granular access logs for post-compromise analysis and compliance with data protection acts (GDPR, HIPAA, SOC 2). The access logs are respectful of privacy, and are not available to anyone except you.
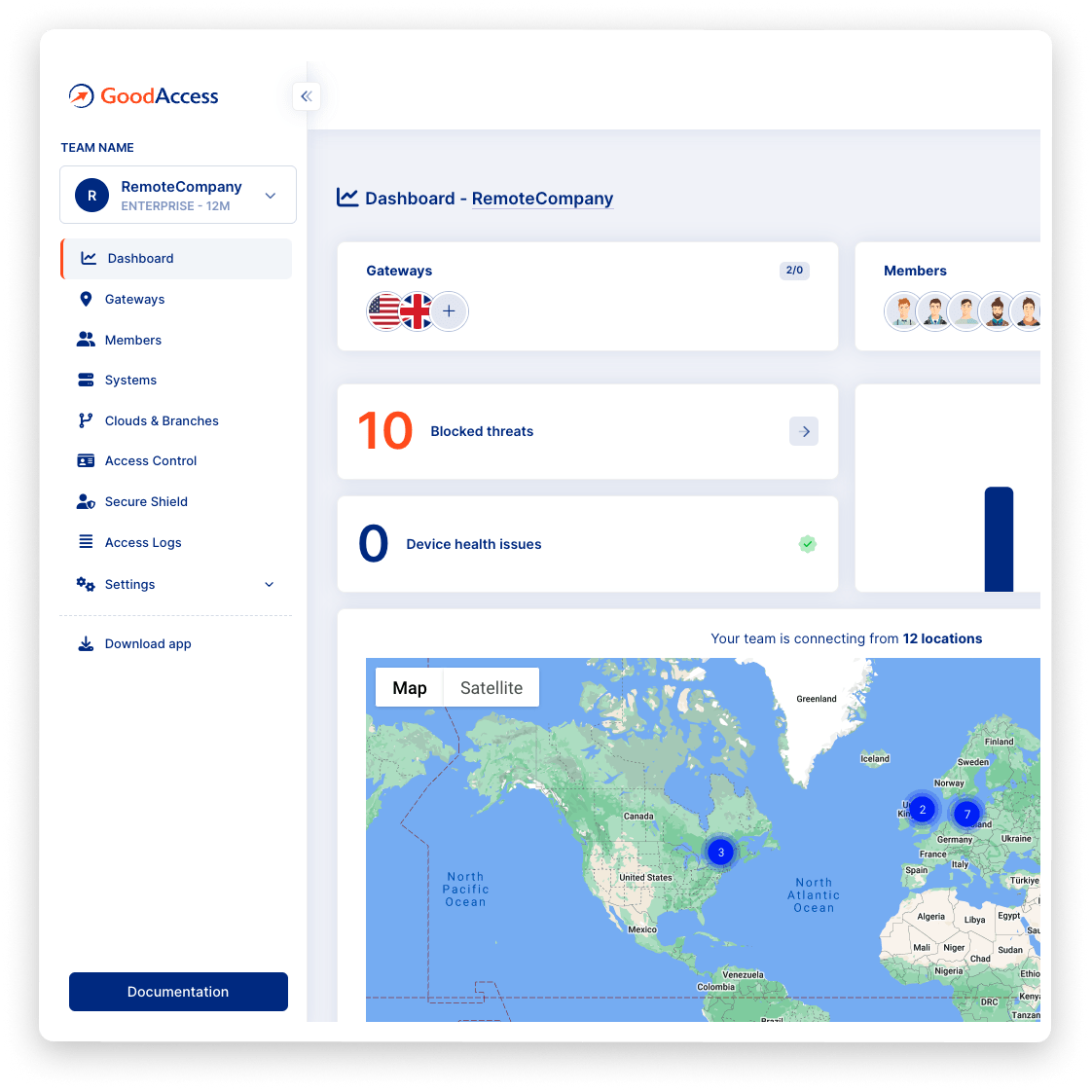
Policy enforcement
Policy enforcement
Block attempts to access malicious or banned websites and services on the domain level. Keep track of non-compliant devices and policy breaches on the dashboard.
zero-hardware solution
Flexible, zero-hardware solution
Connect all devices, locations, and systems in one secure zero-trust environment. Ensure a consistent level of security, whether you are accessing LAN, private/public cloud, or SaaS application from an internal network, home, or hotel wi-fi.
Case study
Hear it from your peers


Case study
Zero Trust Architecture in Creative Dock
Creative Dock needed to ensure ISO 27001 compliance, but they
struggled to achieve the required level of security and control over their network and
user devices (BYOD) with their prior remote-access solution.
Without any additional hardware, GoodAccess provided Creative Dock with full,
centralized control over their infrastructure and
covered up to 70% of technical security requirements of ISO 27001.

Trusted leader in Zero Trust Security
Discover why leading companies rely on GoodAccess for building their Zero Trust Architecture solutions.

"Incredibly user frienly, fast and very helpful."
Overall, the GoodAccess platform is amazing. From the administration side, the platform is incredibly user friendly and you can be up and running in a few minutes, managing users takes no time at all and the customer service is fast and very helpful. We have been with GoodAccess for a number of years with no complaints. The product is very competitive in price with its competitors.

"Find the connectivity and stability of connections stable."
We have been very happy with the reliability of GoodAccess. We find the connectivity and stability of connections stable, we have users across multiple countries and the experience has been very good.

"Simplifies access management and reduces network administration complexity."
GoodAccess's Zero Trust Architecture effectively secures our access to critical network infrastructure and web applications. By enabling a unified IP address for all clients, it simplifies access management and reduces network administration complexity.


"Secure, scalable access to critical systems across a global IP reach."
GoodAccess provides fast onboarding, excellent reporting, and helpful support. It offers secure, scalable access to critical systems across a global IP reach, making it vital for managing multiple users effortlessly. The platform's user-friendly management enhances our operational efficiency and security.

How to enable zero trust network access with GoodAccess

Test all premium features for 14 days without limitation. No credit card required.

Connect to a gateway near your location, decide what systems to include in your secure environment.

Invite team members and set up 2FA. Assign access cards with privileges to each user role.
Get your personalized product demo
Take a product tour with Eva, GoodAccess product expert, to discover how GoodAccess meets your needs firsthand.

Other features
Explore other features

Two-factor authentication
Prevent unauthorized access to your internal systems with two-factor pre-authentication and biometrics.


Dedicated VPN gateway
Connect from anywhere in the world via a secure and private tunnel.


Network access control
Extend full control over inbound connections, manage them centrally with zero hardware required.

zero trust network access guide
A complete guide to zero trust network access in GoodAccess
Authentication
GoodAccess pre-authenticates users and their devices when they log into the secure GoodAccess infrastructure. The login supports multi-factor authentication (MFA), with biometrics and tokens, and single sign-on (SSO) using Google, Okta, MS Entra ID credentials, or universal (SAML).
Authorization
Once a user is authenticated, GoodAccess grants them access privileges to a pool of allowed systems. This access is granted on the network layer, which protects other systems from unauthorized entry.
Segmentation
Access privileges are granted via virtual
access cards
. You can attach company systems (SaaS apps, clouds, servers, LANs) to an access card
corresponding to a particular company role and then assign the card to the users performing
that role.
A user may hold several cards. You can add or remove privileges with a click of the mouse
and build a layered network ecosystem consisting of multiple access environments that contain
a threat early in the event of a compromise.
Read more about zero-trust network access in this article.

