Secure web gateway for small and medium teams
Stop phishing, malware, botnets, and other online security threats before they hit the user and breach your network. All automated with GoodAccess Threat Blocker, a secure web gateway.
Create Free Account See DemoNo card required. Full onboarding support.




BENEFITS
Shield your organization from web-based threats

Breach prevention
Prevent users from accessing dangerous or compromised websites and falling prey to malware, phishing, C&C botnets and other ploys.

Always-on guard
No matter where the user is, once they connect through the GoodAccess secure web gateway, they are protected.

Flexibility
Customize your security by adding your own rules and unwanted sites on top of built-in threat intelligence feeds.

Full control
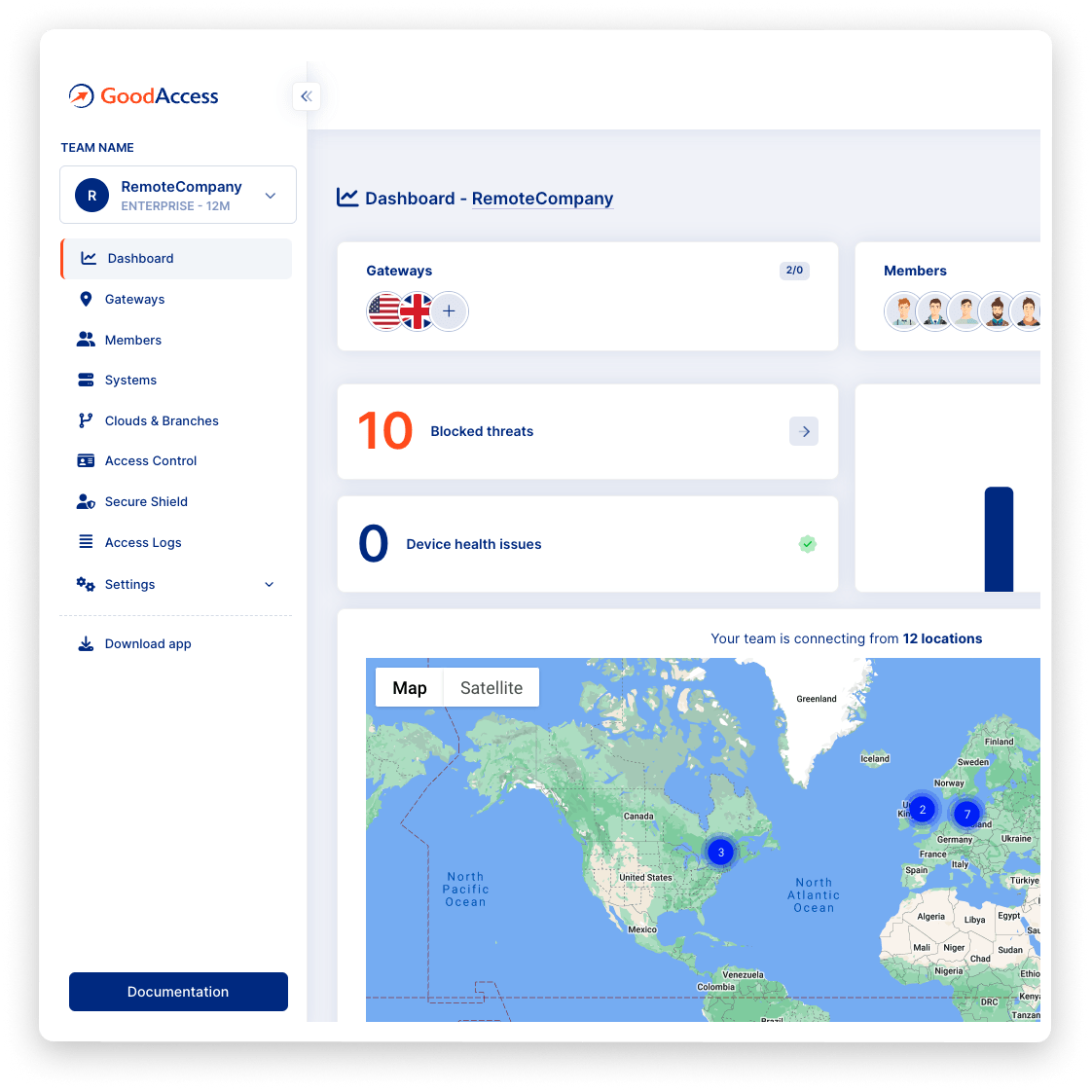
Monitor users' attempts to make malicious connections on the dashboard, isolate the threat and respond confidently.
Try Interactive Demo
Experience GoodAccess via an interactive demo. Get a feel for all its features and find out why GoodAccess is the right choice for your business.
FEATURES
No matter where the user is, with Threat Blocker they are protected
threat blocker
Threat intelligence feeds
Threat Blocker uses a large database of threat intelligence feeds, covering malicious sites, malware, spammers, C&C botnets, and other types of online threats. Custom blacklists are supported to fine-tune your controls.
secure gateway
Secure web gateway
Once a user connects through a cloud gateway with your dedicated DNS server, all of their web activity is protected in real time by blocking unwanted content and malicious domains (see DNS filtering).

threat control
Threat visibility & control
For monitoring and compliance reasons, users' access to harmful websites and content is tracked and logged. See which users attempted to access blocked or harmful sites to isolate the threat, respond, and optimize your security controls.
Mobile & desktop apps
Mobile and desktop apps
GoodAccess comes with one-click apps for iOS, macOS, Android, Windows and ChromeOS. No configuration is needed. Just invite your colleagues via email to create their account and get the GoodAccess app.
Case study
Hear it from your peers


Case study
Zero Trust Architecture in Creative Dock
Creative Dock needed to ensure ISO 27001 compliance, but they
struggled to achieve the required level of security and control over their network and
user devices (BYOD) with their prior remote-access solution.
Without any additional hardware, GoodAccess provided Creative Dock with full,
centralized control over their infrastructure and
covered up to 70% of technical security requirements of ISO 27001.

Trusted leader in Zero Trust Security
Discover why leading companies rely on GoodAccess for building their Zero Trust Architecture solutions.

"Incredibly user frienly, fast and very helpful."
Overall, the GoodAccess platform is amazing. From the administration side, the platform is incredibly user friendly and you can be up and running in a few minutes, managing users takes no time at all and the customer service is fast and very helpful. We have been with GoodAccess for a number of years with no complaints. The product is very competitive in price with its competitors.

"Find the connectivity and stability of connections stable."
We have been very happy with the reliability of GoodAccess. We find the connectivity and stability of connections stable, we have users across multiple countries and the experience has been very good.

"Simplifies access management and reduces network administration complexity."
GoodAccess's Zero Trust Architecture effectively secures our access to critical network infrastructure and web applications. By enabling a unified IP address for all clients, it simplifies access management and reduces network administration complexity.


"Secure, scalable access to critical systems across a global IP reach."
GoodAccess provides fast onboarding, excellent reporting, and helpful support. It offers secure, scalable access to critical systems across a global IP reach, making it vital for managing multiple users effortlessly. The platform's user-friendly management enhances our operational efficiency and security.

The best priced offering on the market
Cloud-based secure web gateway that fits your needs.
Full onboarding support.
BASE
Instant deployment
Deploy your private secure cloud network in less than 10 minutes.
Dashboards & Weekly Reports
Oversee your remotely working teams and check the security status of your whole organization.
MSI Deployment
Centralize the distribution of client apps to your team members.
Networking
Dedicated gateway with static IP
Choose from 35+ always-available cloud gateways worldwide, or get a new one on demand. Each gateway comes with a unique static IP and is dedicated just to your organization.
1 Gbps connection / Gateway
Unlimited data usage
Global secure private network
Interconnect your on-site and remote teams via a dedicated private network.
Additional gateways as Add-on
Optimize network performance for your global teams. Ensure 100% availability in case of local network issues.
Split tunneling
Access your critical systems via the secure GoodAccess gateway and route non-essential traffic directly to optimize latency.
Premium SECURE SHIELD
Threat Blocker Premium
Automated defense against malicious domains (malware, ransomware, phishing, botnet C&C, spammers, and more) with built-in threat intelligence feeds, customizable blacklists, and granular threat activity details.
Two-factor authentication
Enforce 2FA on the management interface, client apps, and optionally per every connection.
Gateway-level access logs
Monitor who connects to your network to meet compliance requirements (GDPR, HIPPA, SOC2)
Device Inventory
Keep track of user devices, their parameters, and spot suspicious behaviors.
ZTNA - Zero Trust Network Access for multi-site & cloud businesses
Enterprise features and Premium 24/7 support for large organizations
SOC2 and ISO 27001 certified. GDPR, HIPAA compliant.
GoodAccess adheres to the most demanding standards of software security compliance so you can have a peace of mind that your organization's data is safeguarded properly.
Let's get started
ThreatBlocker is a built-in secure web gateway feature of every GoodAccess subscription plan. Subscribe to any plan to benefit from protection against malware, ransomware, phishing C&C botnets, and robust security and threat monitoring.

Create your free account and get all premium features for 14 days.

Choose from 35+ dedicated VPN gateway locations or connect through a global shared gateway network.

Invite users via email to create their account and get a GoodAccess app (available for iOS, Mac, Android, Windows and ChromeOS).

securely
Click to connect from any device, anywhere and work securely.
Get your personalized product demo
Take a product tour with Eva, GoodAccess product expert, to discover how GoodAccess meets your needs firsthand.

FAQs
A secure web gateway (SWG) is an application-level traffic filtering solution that monitors all requests between users and web servers on the internet. A SWG was traditionally deployed on the network perimeter. Today, cloud-delivered solutions are more common, as users work from home or use unsecured wifi networks, to protect every employee from malware, phishing, botnet C&C, or other online threats.
The SWG checks user attempts to communicate with a domain against a blacklist, either commercial, open source, or a custom list of forbidden services based on company policies and automatically blocks suspicious traffic.
Firewall, being a perimeter security measure just like the SWG,
works traditionally on a network level, blocking unwanted traffic
based on IP, port, protocol, geographical information, packet size
etc. The SWG, on the other hand, works on the application layer,
at HTTP and DNS requests, searching for attempts to connect to
specific domains or hosts.
Modern firewalls, so-called
"next-gen firewalls" are a unified package of different features
for threat detection and prevention, identity-based inspections,
spam filters, and more. Sometimes they also include a secure web
gateway functionality. Lightweight architectures for modern
perimeter-less do not favor robust all-in-one firewalls and the
secure web gateway is more often a part of remote-access solutions
for cloud-first deployments.
If you need a dedicated VPN gateway with a static IP address for IP whitelisting, you will need one of GoodAccess paid plans (Essential and higher). Learn more in our blog on IP whitelisting.
With our 14-day free trial you can try all the premium features of GoodAccess. Once the 14 days trial period expires, you have to switch to one of the paid plans or go with Starter.
There are no bandwidth caps when using GoodAccess. Thanks to the global gateway network, our users do not experience latency issues.
The security of GoodAccess and its users is of paramount importance to us. This is why we put significant emphasis on protection of our gateways, which are protected against brute-force attacks and other malicious techniques, encryption protocols, algorithms, and authentication methods. Our solution is subjected to continual penetration tests from two different cyber security companies and complies with GDPR. Visit our website on security of GoodAccess to learn more.

