GDPR Certification
The General Data Protection Regulation (GDPR) is an EU legislation that governs how data
controllers and data processors handle user data, and grants rights to data
subjects (users, customers). Compliance with the GDPR is a critical prerequisite of doing any
kind of business in the EU's online space, whether you are based in the EU or collect information from
EU citizens.
GoodAccess is a fully GDPR compliant company based in the EU and bound by its laws. Our
ZTNA-as-a-service solution can help you meet GDPR criteria of access control and monitoring.
No card needed. Full onboarding support.





Why us?
Why GoodAccess
What is GDPR compliance
Responsibilities under GDPR
GDPR is a comprehensive set of regulations that governs how companies collect, store, and use customer data. Article 5 of the GDPR lists seven key principles related to the processing of personal data that data controllers and data processors must follow:
- ● Lawfulness, fairness, and transparency,
- ● Purpose limitation,
- ● Data minimization,
- ● Accuracy,
- ● Storage limitation,
- ● Integrity and confidentiality,
- ● Accountability.
As pertains to electronic data, data controller and processor responsibilities include, but are not limited to, the following:
Preserve privacy
Data management
According to GDPR guidelines, data must be collected with the data subject's consent, anonymized to preserve privacy, and deleted upon the data subject's request (aka "right to be forgotten").
access controls
Data security
Data controllers and processors must deploy robust security measures and access controls to safeguard personal data, ensuring its confidentiality, integrity, and availability, both in storage and during transfer.
gdpr guidelines
Breach notification
According to GDPR guidelines, data breaches must be promptly reported to the relevant authorities and, where relevant, to data subjects affected.
access history
Activity logging
Access history to subjects' data must be thoroughly logged. Under GDPR, user activity logs must be anonymous and kept for no greater period than strictly necessary.
GDPR compliance
GoodAccess can help you with GDPR compliance
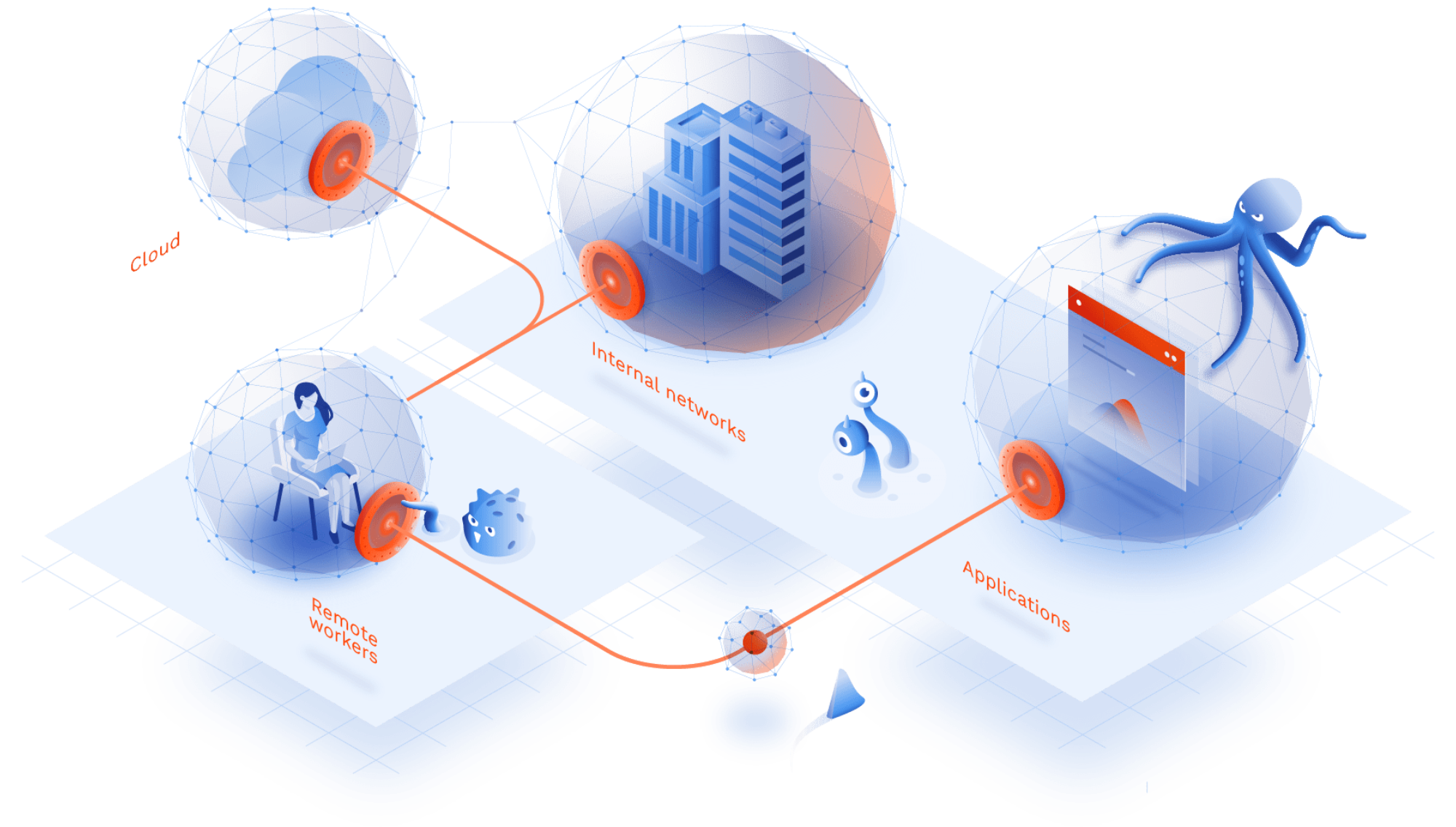
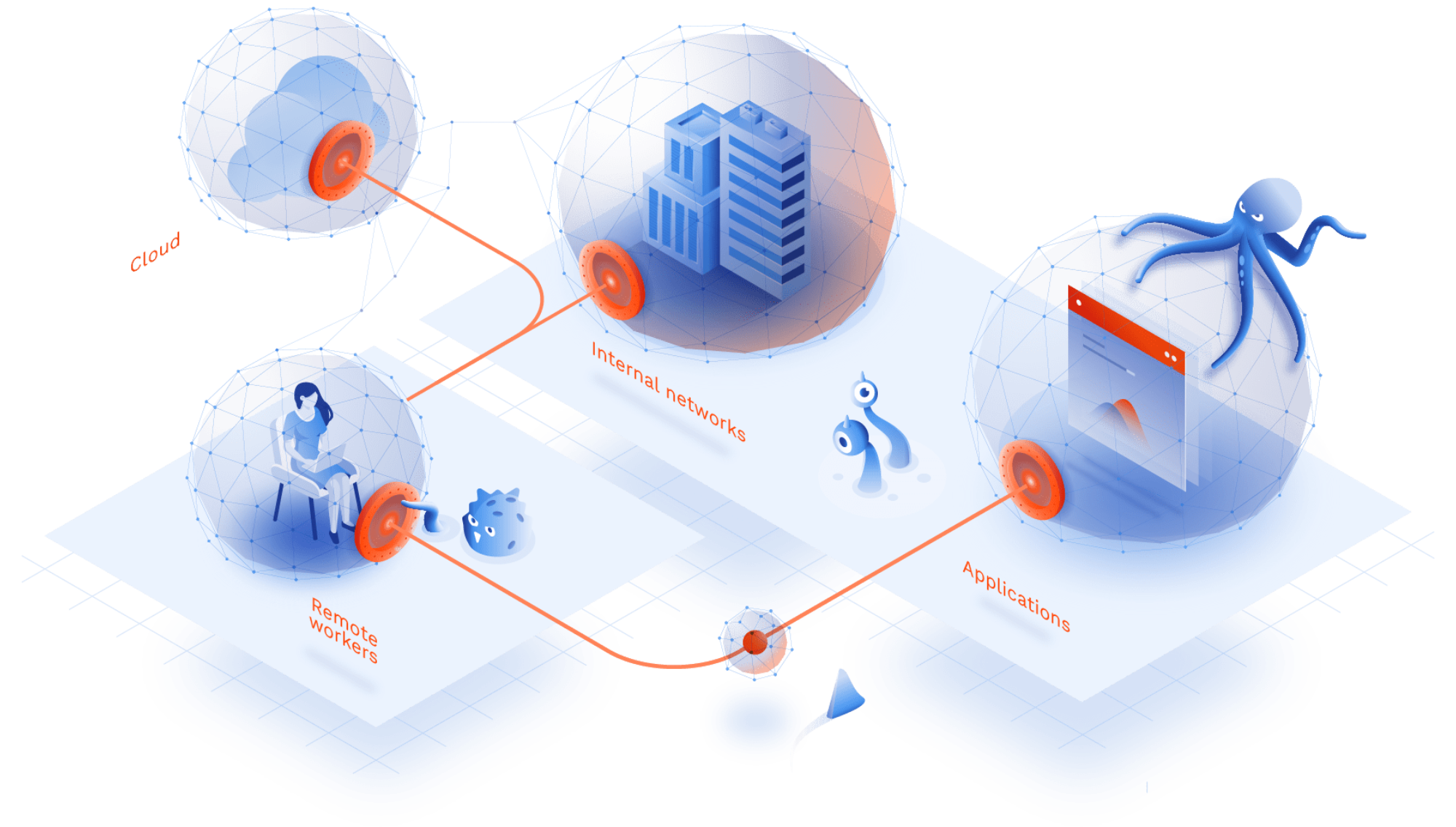
GoodAccess provides zero-trust as a service, which is a network security solution that can help you cover some requirements set by GDPR.
Access control
GoodAccess features a robust yet user-friendly access control mechanism that allows you to assign and manage the access rights of individual users as well as groups. This enables you to prevent unauthorized access to digital resources to all users who lack the appropriate privileges.
Access monitoring
GoodAccess keeps system-level access logs that tell you which user has accessed which resource and when, including information on session length and the volume of data transferred. Keeping track of access history to the data your curate is an important component of GDPR compliance.
testimonials
See why your peers choose GoodAccess
Benefits
Why GoodAccess is your go-to compliance solution
GoodAccess is a SOC 2 certified customer choice among cloud-based zero-trust solutions. We are fully GDPR, HIPAA compliant and have passed ISO 27001 and SOC 2 certification.
Device posture check & management
Filter out non-compliant devices to reduce the risk of breaches. Define your device security policy and enforce it from the central console.
Identity-based access control
Assign access on a least-privilege and per-app basis centrally and easily.
Software-defined perimeter
Apply a protective layer over all your users and resources, wherever they are. Enforce the same level of security throughout multi-site and multicloud environments.
Cryptography and encryption
Protect data and user identity during transit with strong, unbroken encryption.
Auditable access logs
Monitor activity on the level of systems and gateway, locate breaches and configuration issues, feed the logs to a SIEM.
Multi-factor authentication
Prevent unauthorized access with MFA before allowing access to internal systems.
Business continuity
Configure your secure GoodAccess secure environment in high-availability to ensure continuous protection.
Vulnerability disclosure
We are open about our limits. GoodAccess is an essential component of your security ecosystem that complements other security solutions.

Security policies
Enforce your security policy centrally and ensure no user accesses critical resources without satisfactory authorization.
Start your transition today




Get your personalized product demo
Take a product tour with Eva, GoodAccess product expert, to discover how GoodAccess meets your needs firsthand.